What’s Occurred in Web Years?
I was trying to explain to a colleague some of the sea change that has already taken place on the web (IMHO) – “Web 2.0” if you will?
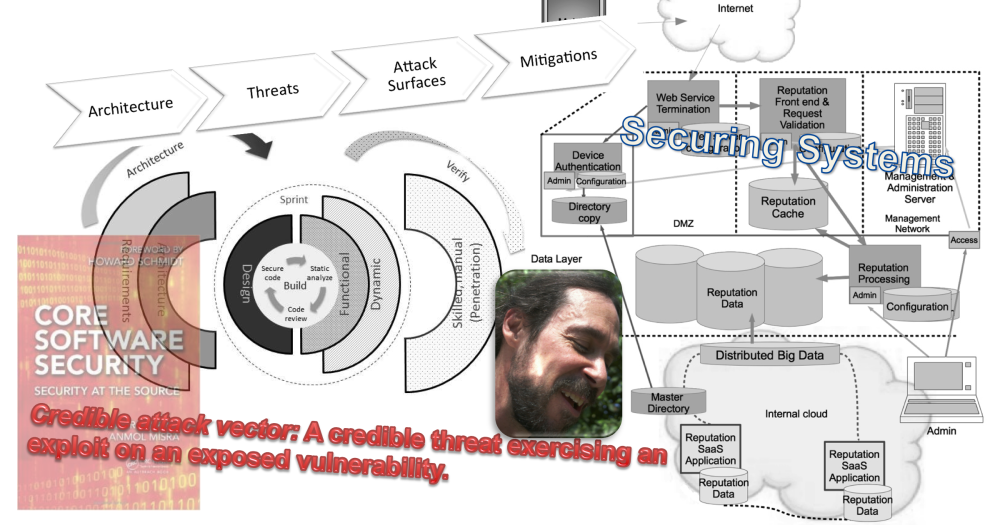
I was explaining that the typical large enterprise (and really, many small ones, too) have become an intersection of clouds.
We used to use the image of the “good” inside protecting itself from the hostile (“bad”) Internet. The Internet was the cloud, the internal network a known and fixed space, “the network”. And, indeed, when I got started in Information Security, that is pretty much how things were.
But where I work, nobody knows all the networks that are interconnected. Acquisitions, test networks, global points of presence (POPs), all work to make a complex of interconnected networks. It’s too complex to hold in the mind. A mapping exercise some years ago revealed connections that nobody had documented – “discovered lands!”
In fact, the enterprise network seems a mini-internet or cloud that is probably less hostile than the Internet. But it’s certainly not trusted like the little “Class C” (anybody remember classed networks?) that I use to be responsible for where I knew everyone on the network and a lot of what they were using the network for.
But the enterprise cloud is not the only cloud at play.
Within the business eco-system are many similar interconnected network spaces of varying regulation and relationship, from close to pretty distant and untrusted. To be sure, a lot of these connect via the Internet. But certainly not all. Most enterprises have private connections with partners. The partners are literally cross-connected to the “internal” network.
There may be (should be?) network and other restrictions in place between the networks. Still, traffic flows and presumably some portion of that traffic is likely hostile (hopefully a minute portion, well monitored?)
The need to model business relationships via the network has caused an explosion of interconnected clouds.
Basically, the perimeter means much less than it once did – perhaps even “The perimeter is dead. Long live the perimeter!”
Coupled with this change has been the rapid growth of software tools on the network that model human relationship graphs and which allow a much greater degree of participation.
So, while the internal network has been growing in complexity and opening up to interconnections, usage patterns (and business demand, it turns out) have been driving from inside to out.
These two forces have already occurred. And they happened, to my observation, faster than the growth of Web 1.0. Social networking seems to me to have taken off in months. The blogosphere has well been in place for several years. When is the last time you bought an expensive item about which you were uncertain without first checking online reviews and perhaps the blogosphere? I almost always (always?) do this before uncertain purchases.
What does this all have to do with security architecture?
These changes shift things fundamentally.
Network controls are now a tool – not the basis for one’s information security posture. We are using them around critical assets, but they no longer divide the “good” inside from the “bad” outside.
Meanwhile, data is moving out of the inner cloud and is a “must” for business agility. We can’t control our data by keeping our hot little security controls (“ACLs” – smile) around it.
The old security paradigm is obsolete. We need a new one.
And all this, in my opinion, transpired in web years while many of us were sleeping away building better network castles.
cheers,
/brook
(from the Denver airport)